Nobody seems to know just yet where the massive cyberattack that made major websites like Twitter and Spotify unavailable Friday morning originated. But whether the huge distributed denial of service (DDoS) attack originated in Russia, China, Eastern Europe or right here in the U.S., it’s a reminder of how vulnerable the infrastructure that our increasingly interconnected society relies on is, and makes the increasing willingness of government actors to engage in cyberattacks extremely worrying.
Friday’s attack was aimed at Dyn, a domain name service provider that channels internet traffic to its clients. The company’s systems were overwhelmed briefly Friday by huge numbers of requests made simultaneously with the aim of crowding out legitimate web traffic.
Related: Is This the Real Reason Putin Is Interfering With the US Election?
Early Friday morning, the company reported, “we began monitoring and mitigating a DDoS attack against our Dyn Managed DNS infrastructure. Some customers may experience increased DNS query latency and delayed zone propagation during this time.”
“This attack is mainly impacting US East and is impacting Managed DNS customers in this region,” Dyn reported. An outage map, produced by the telecommunications company Level 3, confirmed massive problems across almost the entire eastern half of the United States.
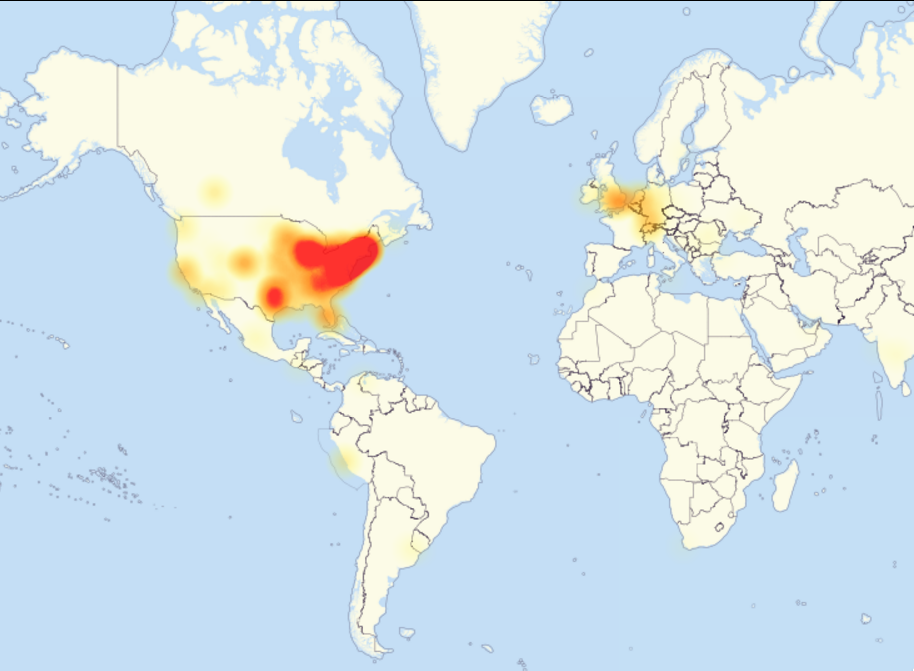
Source: DownDetector via Gizmodo
By mid-morning, engineers had brought the problem largely under control, the company said, and service had been restored.
But while people across the country may be able to tweet and stream music again, the uncomfortable reality is that attacks like this one -- and perhaps even far more destructive ones that involve destruction of data, crippling of critical infrastructure and worse -- are an increasingly real threat.
Related: Clinton Admits She Didn’t Consider the Consequences of Using a Private Email Server
Of course, the attack on Dyn may not have been motivated by any political actors at all. Cybersecurity blogger Brian Krebs, whose own blog was the target of a massive DDOS attack just a few weeks ago, noted, “The attack on DYN comes just hours after DYN researcher Doug Madory presented a talk on DDoS attacks in Dallas, Texas at a meeting of the North American Network Operators Group (NANOG).” That at least raises the possibility that the attack might simply have been hackers trying to embarrass a high-profile security expert.
But regardless of the genesis of this particular attack, the willingness of the Russian government to actively interfere in the U.S. presidential election, to cite the most obvious example, has signaled a dramatic change in the role government cyberwarriors are likely to play in the future. The persistent leaking of hacked emails and other data, stolen from people with ties to the Democratic Party, may be unprecedented, but isn’t likely to remain unique.
The issue even found its way into the final presidential debate, in which Hillary Clinton, the Democratic presidential nominee, pointed out the unanimous assessment of U.S. intelligence agencies which, she said, “all concluded that these espionage attacks, these cyberattacks, come from the highest levels of the Kremlin. And they are designed to influence our election.”
And the U.S. is expected to take some sort of retaliatory action, as Vice President Joe Biden said on Meet the Press last Sunday.
Related: US Makes It Official: Russia Is Hacking the Election
“We’re sending a message -- we have the capacity to do it,” Biden said.
“He'll know it,” Biden continued, referring to Russian President Vladimir Putin. “It will be at the time of our choosing. And under the circumstances that have the greatest impact.”
While the U.S. can hardly avoid mounting some sort of response, the worry is that it could lead to an escalating series of retaliatory actions and frequent disruptions that could play havoc with an economy that has become dependent on unfettered, reliable connectivity.
During the Cold War, for better or worse, there was an effective brake on escalation in the form of nuclear weapons. Russia and the U.S. tried to avoid direct conflict, in large part out of fear that military engagement might spiral out of control, leading to the very real possibility of mutual destruction.
In cyberwarfare, so far at least, there is no obvious equivalent to an intercontinental nuclear missile. And while that’s probably a good thing, on balance, it also means that there is no obvious line that everyone involved has an interest not only in not crossing, but not even approaching.





